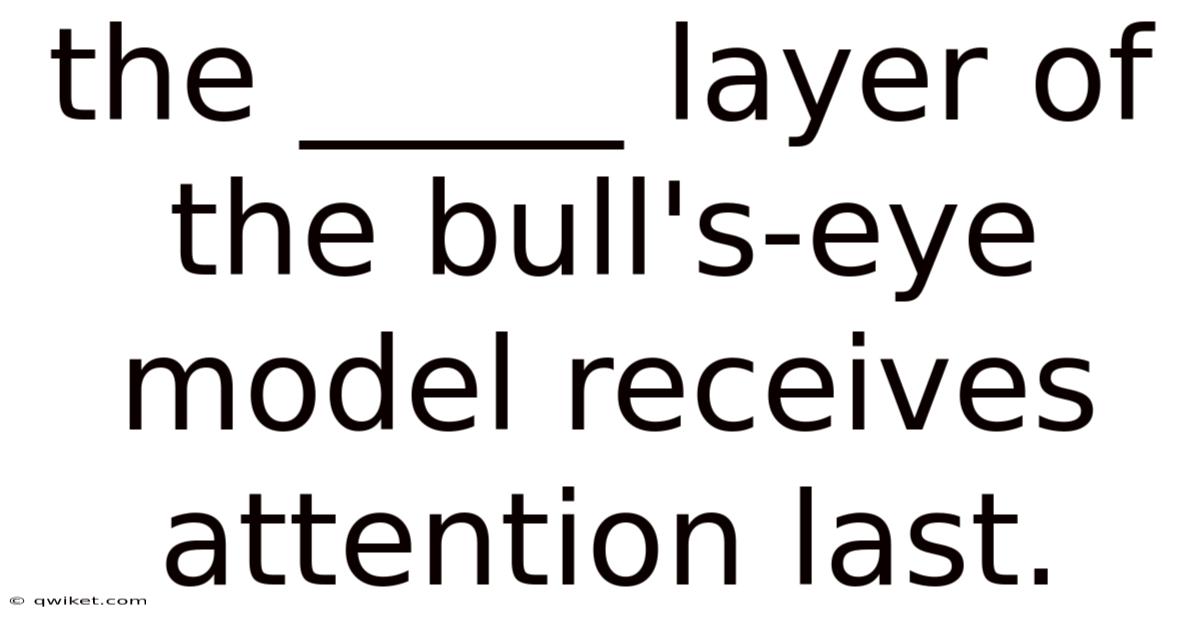
The Application Layer of the bull's-eye model receives attention last, and for good reason. This layer represents the outermost ring of the model, where security measures are applied after the core systems and infrastructure have been secured. Understanding the significance of this layer is crucial for anyone involved in cybersecurity, network management, or IT infrastructure planning.
The bull's-eye model, also known as the defense-in-depth approach, is a strategic framework used to prioritize security efforts. It consists of concentric circles, each representing a different layer of an organization's IT infrastructure. That's why the innermost circle typically includes the most critical assets, such as data and core applications. As you move outward, the layers become less critical but still essential for overall security Nothing fancy..
The Application Layer, being the outermost layer, is where user-facing applications and services reside. Now, this includes web applications, mobile apps, and other software that interacts directly with end-users. While it might seem counterintuitive to address this layer last, there are several compelling reasons for this approach Nothing fancy..
Firstly, by securing the inner layers first, organizations create a strong foundation for their security posture. This foundation includes dependable network security, hardened operating systems, and protected data storage. Once these core elements are in place, attention can then be turned to the Application Layer without compromising the overall security of the system.
Some disagree here. Fair enough.
Secondly, the Application Layer is often the most dynamic and frequently changing part of an IT infrastructure. New features are constantly being added, updates are regularly deployed, and user requirements evolve over time. By addressing this layer last, organizations can see to it that their security measures are flexible and adaptable to these ongoing changes.
Worth pausing on this one.
Worth adding, many vulnerabilities in the Application Layer can be mitigated by strong security practices in the lower layers. And for example, a well-configured firewall can block many common attack vectors before they even reach the application level. Similarly, solid authentication and authorization mechanisms at the network level can prevent unauthorized access to applications Practical, not theoretical..
That said, this doesn't mean that the Application Layer should be neglected or given minimal attention. On top of that, on the contrary, once the inner layers are secured, a significant amount of resources and expertise should be devoted to securing this layer. This includes implementing secure coding practices, conducting regular security audits, and employing application-level firewalls and intrusion detection systems And it works..
Among the key challenges in securing the Application Layer is the rapid pace of technological change. New types of applications, such as cloud-based services and Internet of Things (IoT) devices, are constantly emerging. Each of these new technologies brings its own set of security considerations that must be addressed.
Another important aspect of securing the Application Layer is user education and awareness. Since this layer is closest to the end-user, human factors play a significant role in its security. Training users to recognize phishing attempts, use strong passwords, and follow security best practices can greatly enhance the overall security of the Application Layer Still holds up..
Worth pausing on this one.
It's also worth noting that the Application Layer is often the target of sophisticated attacks, such as SQL injection, cross-site scripting (XSS), and other web application vulnerabilities. These attacks can be particularly damaging because they can bypass lower-level security measures and directly compromise sensitive data or system functionality.
To effectively secure the Application Layer, organizations should implement a multi-faceted approach. This includes:
-
Regular security testing: Conducting penetration tests and code reviews to identify and address vulnerabilities Still holds up..
-
Patch management: Keeping all applications and their dependencies up to date with the latest security patches.
-
Input validation: Implementing strict input validation to prevent common attacks like SQL injection and XSS Simple, but easy to overlook..
-
Encryption: Using strong encryption for data in transit and at rest to protect sensitive information Easy to understand, harder to ignore. Nothing fancy..
-
Access controls: Implementing strong authentication and authorization mechanisms to confirm that only authorized users can access applications and their data.
-
Monitoring and logging: Setting up comprehensive monitoring and logging to detect and respond to security incidents quickly.
-
Incident response planning: Developing and regularly testing incident response plans specific to application-level security breaches.
To wrap this up, while the Application Layer of the bull's-eye model receives attention last, it is by no means the least important. In fact, its position as the outermost layer makes it a critical component of an organization's overall security strategy. By building a strong foundation with the inner layers and then focusing on the Application Layer, organizations can create a comprehensive and effective security posture that protects against a wide range of threats The details matter here..
The key to success lies in understanding that security is not a one-time effort but an ongoing process. As new threats emerge and technologies evolve, the approach to securing the Application Layer must also adapt. By staying informed about the latest security trends and best practices, organizations can check that their Application Layer remains solid and resilient in the face of ever-changing cyber threats.
The Application Layer, while often perceived as the final frontier in security planning, is in fact a dynamic and evolving battleground. Here's the thing — its complexity and direct interaction with users make it both a critical asset and a potential vulnerability. As organizations continue to innovate and adopt new technologies, the Application Layer must be fortified with the same rigor as the foundational layers beneath it.
One of the most effective strategies for securing the Application Layer is fostering a culture of security awareness among users. Which means human error remains one of the leading causes of security breaches, and even the most sophisticated technical defenses can be undermined by a single click on a malicious link or the use of a weak password. Regular training sessions, simulated phishing exercises, and clear communication about security policies can empower users to act as the first line of defense It's one of those things that adds up. But it adds up..
Also worth noting, the rise of cloud-based applications and third-party integrations has expanded the attack surface of the Application Layer. Organizations must now consider not only the security of their own applications but also the trustworthiness of external services and APIs they rely on. This requires a thorough vetting process for third-party vendors and continuous monitoring of their security practices.
Another critical aspect is the adoption of secure coding practices. Developers must be trained to write code that is resilient to common vulnerabilities, such as buffer overflows, race conditions, and improper error handling. Automated tools for static and dynamic code analysis can help identify potential weaknesses early in the development process, reducing the risk of exploitation.
As the threat landscape continues to evolve, so too must the strategies for securing the Application Layer. Emerging technologies like artificial intelligence and machine learning offer new opportunities for enhancing security, from anomaly detection to automated threat response. Still, these same technologies can also be weaponized by attackers, necessitating a proactive and adaptive approach to security.
In the end, the security of the Application Layer is not a destination but a journey. It requires a commitment to continuous improvement, a willingness to adapt to new challenges, and a recognition that every layer of the bull's-eye model is interconnected. By prioritizing the Application Layer and integrating it easily into a holistic security strategy, organizations can build a resilient defense that stands strong against the ever-present and ever-changing threats of the digital age That's the part that actually makes a difference. And it works..
Beyond technical safeguards and user education, reliable logging and monitoring are very important. Think about it: detailed logs provide invaluable forensic data in the event of a breach, allowing security teams to understand the attack vector, scope of compromise, and potential impact. That said, real-time monitoring, coupled with Security Information and Event Management (SIEM) systems, can detect anomalous behavior and trigger alerts, enabling rapid response and containment. This isn’t simply about collecting data; it’s about analyzing it effectively, often leveraging behavioral analytics to identify deviations from established baselines that might indicate malicious activity Most people skip this — try not to..
Adding to this, the principle of least privilege should be rigorously applied. Because of that, users and applications should only have access to the resources they absolutely need to perform their functions. This limits the potential damage an attacker can inflict, even if they manage to compromise an account or application. Implementing multi-factor authentication (MFA) adds another layer of security, making it significantly harder for attackers to gain unauthorized access, even with stolen credentials Still holds up..
Web Application Firewalls (WAFs) remain a crucial component of Application Layer security. Day to day, these firewalls act as a shield, filtering malicious traffic and protecting against common web attacks like SQL injection and cross-site scripting (XSS). That said, WAFs are not a “set it and forget it” solution. They require ongoing tuning and updates to remain effective against evolving attack techniques.
The shift towards DevOps and continuous integration/continuous delivery (CI/CD) pipelines necessitates a “security-as-code” approach. Because of that, integrating security checks directly into the development pipeline – often referred to as DevSecOps – allows vulnerabilities to be identified and addressed early in the process, before they reach production. This proactive approach is far more efficient and cost-effective than attempting to patch vulnerabilities after deployment.
At the end of the day, securing the Application Layer demands a multifaceted strategy that encompasses user awareness, secure coding practices, vigilant monitoring, reliable access controls, and the integration of security throughout the entire software development lifecycle. In real terms, it’s a dynamic process, requiring constant adaptation and investment. Ignoring this critical layer leaves organizations exposed to a significant and growing risk. A strong Application Layer defense isn’t just about preventing breaches; it’s about building trust with customers, maintaining brand reputation, and ensuring the long-term viability of the business in an increasingly interconnected and hostile digital world Worth keeping that in mind..